Cx Programmer Update Download
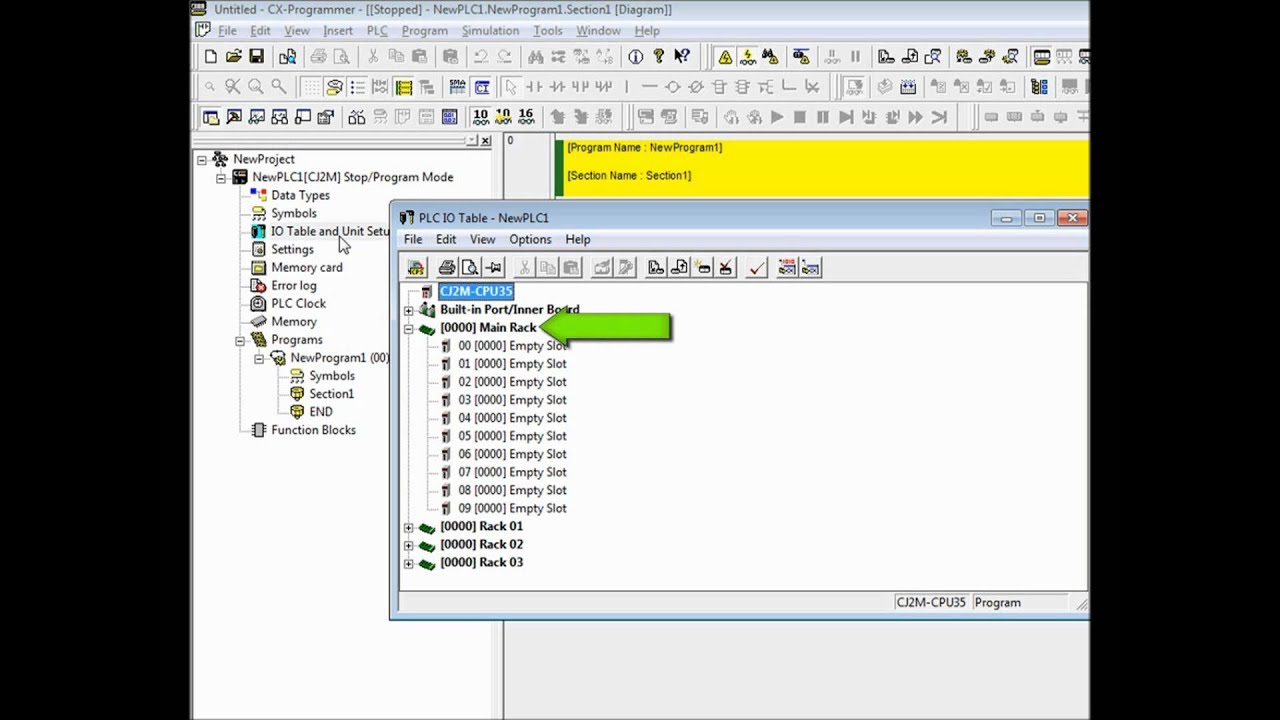
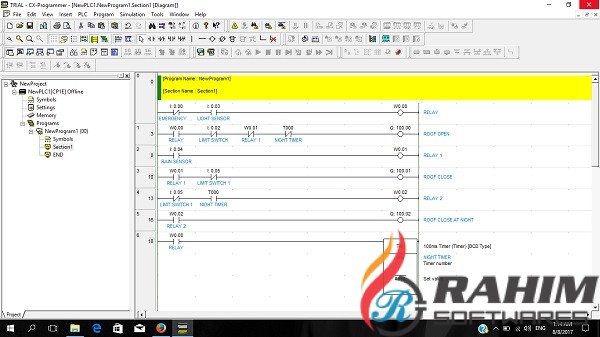
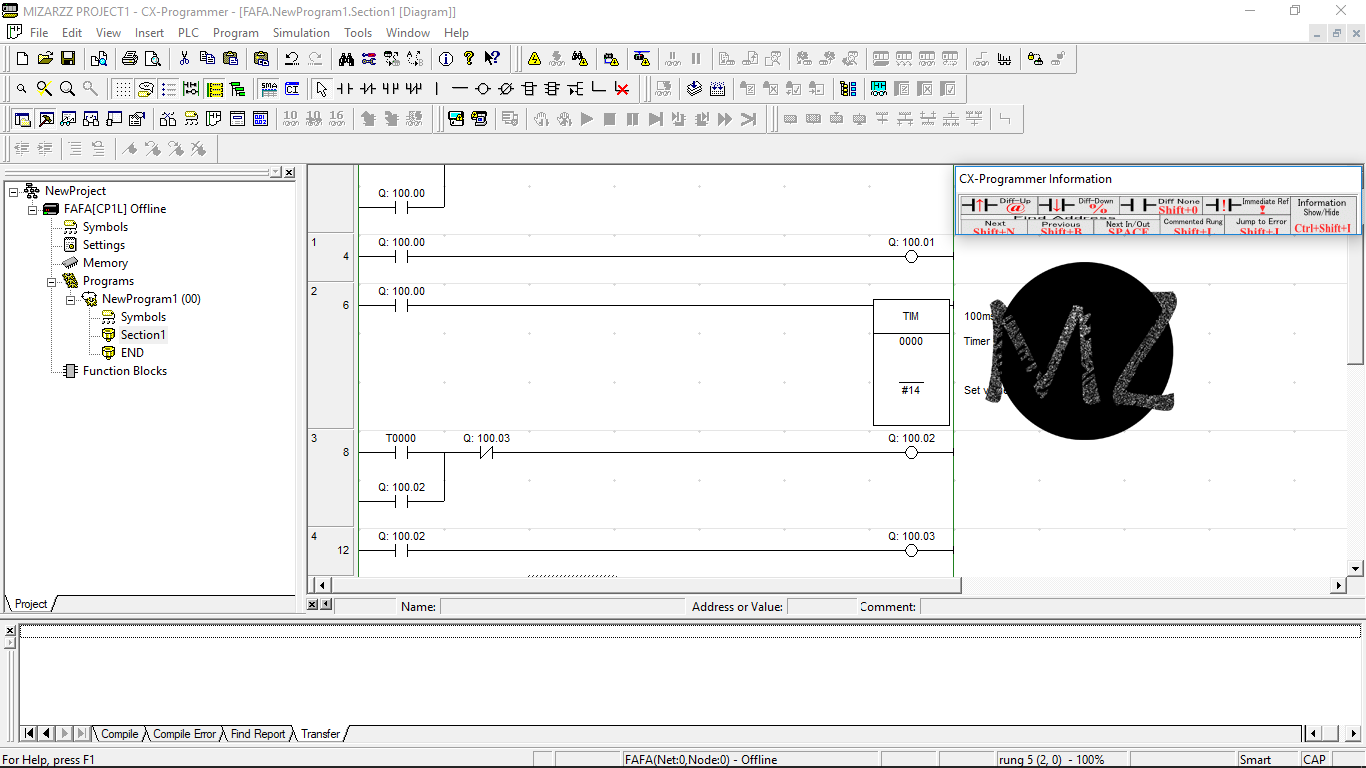
Download; Power Vision CX Update Client (1.60 MB) 1.60 MB: Power Core Software Suite (WinPEP 8 Data Center & Dyno Control, C3 Tuning Software, POD-300. Omron CX-One Full Free enables users to build and host one application like PLC, HMI, motion control systems or network using a single package. Omron is the latest software that provides automation that uses automated system updates or allows users to quickly download or install updates for free. CX-Programmer, the programming software for all Omron's PLC series, is fully integrated into the CX-One software suite. CX-Programmer includes a wide variety of features to speed up the development of your PLC program. New parameter-setting dialogues reduce setup time, and with standard function blocks in IEC 61131-3 structured text.
1. EXECUTIVE SUMMARY
CX-Programmer for CP1E Trial Version is a Shareware software in the category Miscellaneous developed by Blood Pressure Data Manager (CProgram FilesOmronBpm121F). The latest version of CX-Programmer for CP1E Trial Version is currently unknown. It was initially added to our database on. Omron Cx Programmer software, free download » download update cx programmer 9.5 » download cx-programmer 9.5 » download cx programmer 9.5 » download software cx programmer 9.5.
- ATTENTION: Low skill level to exploit
- Vendor: Omron
- Equipment: CX-Programmer within CX-One
- Vulnerability: Use After Free
2. RISK EVALUATION
Successful exploitation of this vulnerability could allow an attacker to execute code under the privileges of the application.
3. TECHNICAL DETAILS
3.1 AFFECTED PRODUCTS
The following version of CX-Programmer within CX-One is affected:
- CX-Programmer v9.70 and prior
- Common Components January 2019 and prior
3.2 VULNERABILITY OVERVIEW
3.2.1 USE AFTER FREE CWE-416
Cx-programmer Update Download
When processing project files, the application fails to check if it is referencing freed memory. An attacker could use a specially crafted project file to exploit and execute code under the privileges of the application.
CVE-2019-6556 has been assigned to this vulnerability. A CVSS v3 base score of 6.6 has been assigned; the CVSS vector string is (AV:L/AC:L/PR:N/UI:R/S:U/C:L/I:L/A:H).
3.3 BACKGROUND
- CRITICAL INFRASTRUCTURE SECTORS: Critical Manufacturing
- COUNTRIES/AREAS DEPLOYED: Worldwide
- COMPANY HEADQUARTERS LOCATION: Japan
3.4 RESEARCHER
Esteban Ruiz (mr_me) of Source Incite, working with Trend Micro’s Zero Day Initiative, reported this vulnerability to NCCIC.
Cx Programmer 9.7
4. MITIGATIONS
Omron has released an updated version of CX-One to address the vulnerability. This release is available through the CX-One auto-update service.
- CX-Programmer Version 9.71
- Common Components April 2019
NCCIC recommends that users take the following measures to protect themselves from social engineering attacks:
- Do not click web links or open unsolicited attachments in email messages.
- Refer to Recognizing and Avoiding Email Scams for more information on avoiding email scams.
- Refer to Avoiding Social Engineering and Phishing Attacks for more information on social engineering attacks.
.jpg)
NCCIC also recommends users take defensive measures to minimize the risk of exploitation of this vulnerability. Specifically, users should:
- Minimize network exposure for all control system devices and/or systems, and ensure that they are not accessible from the Internet.
- Locate control system networks and remote devices behind firewalls, and isolate them from the business network.
- When remote access is required, use secure methods, such as Virtual Private Networks (VPNs), recognizing that VPNs may have vulnerabilities and should be updated to the most current version available. Also recognize that VPN is only as secure as the connected devices.
NCCIC reminds organizations to perform proper impact analysis and risk assessment prior to deploying defensive measures.
NCCIC also provides a section for control systems security recommended practices on the ICS-CERT web page. Several recommended practices are available for reading and download, including Improving Industrial Control Systems Cybersecurity with Defense-in-Depth Strategies.
Additional mitigation guidance and recommended practices are publicly available on the ICS-CERT website in the Technical Information Paper, ICS-TIP-12-146-01B--Targeted Cyber Intrusion Detection and Mitigation Strategies.
Organizations observing any suspected malicious activity should follow their established internal procedures and report their findings to NCCIC for tracking and correlation against other incidents.
No known public exploits specifically target this vulnerability. This vulnerability is not exploitable remotely.
Contact Information
For any questions related to this report, please contact the CISA at:
Email: CISAservicedesk@cisa.dhs.gov
Toll Free: 1-888-282-0870
For industrial control systems cybersecurity information: https://us-cert.cisa.gov/ics
or incident reporting: https://us-cert.cisa.gov/report
CISA continuously strives to improve its products and services. You can help by choosing one of the links below to provide feedback about this product.
Omron Cx Programmer Free Download
This product is provided subject to this Notification and this Privacy & Use policy.
